Our Deepest Source Code Analysis via Static Application Security Testing
TrueCode is like having a hacker proofread your code, to point out all the places where a criminal will be able to sneak in once its on your website. Having this full insight into your application can reveal a wider range of bugs and vulnerabilities than the "trial and error" of traditional vulnerability testing.
Benefits of SiteLock® TrueCode™ SAST
How SiteLock® TrueCode™ Works
Vulnerability Detection in Custom or Third Party Code
Actionable Data
Deep Visibility
Adhere to Regulations
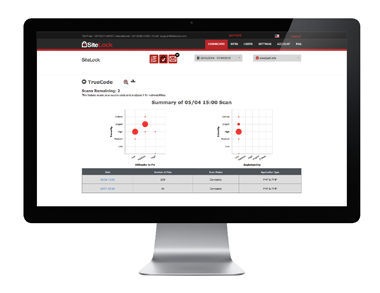
TrueCode Static Application Security Testing (SAST), or "white-box" testing, finds common vulnerabilities by performing a deep analysis of your applications without actually executing them. TrueCode analyzes your source code to create a detailed model of the application's interaction with users and sensitive resources (such as your database or your customers). We then identify all paths through the application that represent a potential weakness. For example, if a data path through the application originates from an HTTP Request and flows through the application without validation or sanitization to reach a database query, then this would represent a SQL Injection flaw. We then deliver actionable information that helps you prioritize flaws according to severity so you can address them quickly.
How does SiteLock® TrueCode™ protect my website?
TrueCode SAST adds a unique and critical layer of security by protecting your web applications— where 92% of vulnerabilities reside. We have taken what has traditionally been a very expensive service available only to large enterprise businesses, and made it easy and affordable for smaller business owners to access.
Identify vulnerabilities and backdoors in custom and third-party code applications 100% comprehensive scanning Examines code from top (interface with the user) to the bottom (interface with the database or OS) Acts like a spell check, highlighting every vulnerability in the code (by line) and simplifying remediation Complies with PCI and other industry guidelines that require a code review Simplifies security by prioritizing the flaws to fix first

